Cryptocurrency has rapidly transformed the landscape of financial transactions, introducing a digital economy that operates independently of traditional banking systems. Central to this digital economy are crypto wallets, essential tools for anyone engaging with cryptocurrencies. They not only facilitate the storage and management of digital assets but also ensure security in the decentralized world of digital currency. This guide delves into the fundamentals of crypto wallets, offering an essential understanding for both newcomers and seasoned users. It provides clarity on their operation, security, and the various types available, making it a crucial read for navigating the crypto space.
What are Crypto Wallets?

A crypto wallet is more than just a storage unit; it’s the gateway to interacting with the blockchain. These wallets don’t store physical coins; instead, they keep digital keys used to access cryptocurrency addresses and sign transactions. This distinction is crucial for understanding how digital currencies operate in a decentralized environment. There are various forms, including software, hardware, and paper wallets, each offering different levels of convenience and security.
The choice between a hot wallet (connected to the internet) and a cold wallet (offline storage) depends on the user’s needs for accessibility versus security. Hot wallets, like mobile or desktop applications, provide ease of access for daily transactions. In contrast, cold wallets, such as hardware or paper wallets, are best for long-term storage due to their reduced vulnerability to online threats. Each type caters to different aspects of cryptocurrency usage, from everyday spending to secure asset holding, making the understanding of their nuances vital.
How Do Crypto Wallets Work?
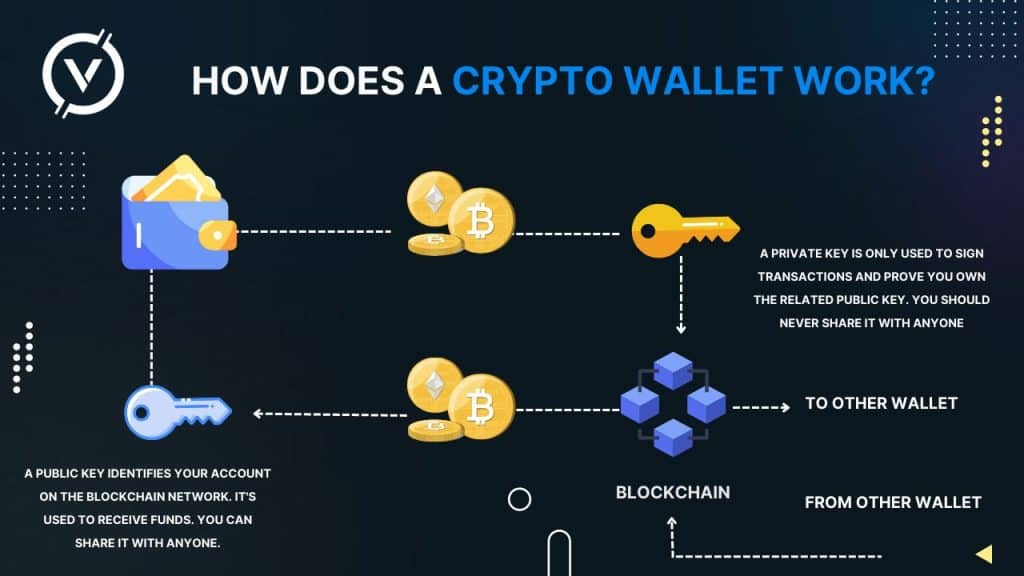
Crypto wallets operate using a pair of cryptographic keys: the public key and the private key. The public key can be shared and is used to receive funds, akin to a bank account number. The private key, however, should remain confidential, as it’s used to authorize transactions and access funds. This key pair is foundational to maintaining security and ownership in the blockchain network.
When a transaction is initiated, it’s signed with the sender’s private key and then verified by the network using the public key. This process ensures that only the rightful owner can spend the cryptocurrencies stored in a wallet. It’s a blend of simplicity and sophisticated cryptography, enabling secure and efficient transactions without the need for intermediaries. The decentralized nature of this system marks a significant shift from traditional financial models, emphasizing user autonomy and security.
Setting Up a Crypto Wallet

Choosing the right crypto wallet is a critical decision, hinging on factors such as the type of cryptocurrency, intended use, and the user’s approach to security. For beginners, software wallets provide a good balance of accessibility and security. However, for larger investments or long-term holding, hardware wallets offer enhanced security. Setting up a wallet typically involves downloading the software or purchasing the hardware device. For software wallets, the process includes creating an account and setting a strong password. Hardware wallets require initializing the device and setting a PIN.
Both types will generate a recovery phrase, which is paramount for accessing funds if the device is lost or the password is forgotten. The recovery phrase, usually a series of 12 or 24 words, acts as a backup key to the wallet. It’s essential to store this phrase securely and privately, as it’s the only way to regain access to the assets if the primary access method is compromised. This setup process underscores the responsibility that comes with managing digital assets, placing significant emphasis on security measures from the outset.